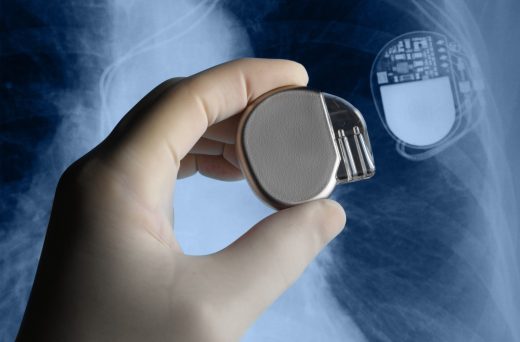
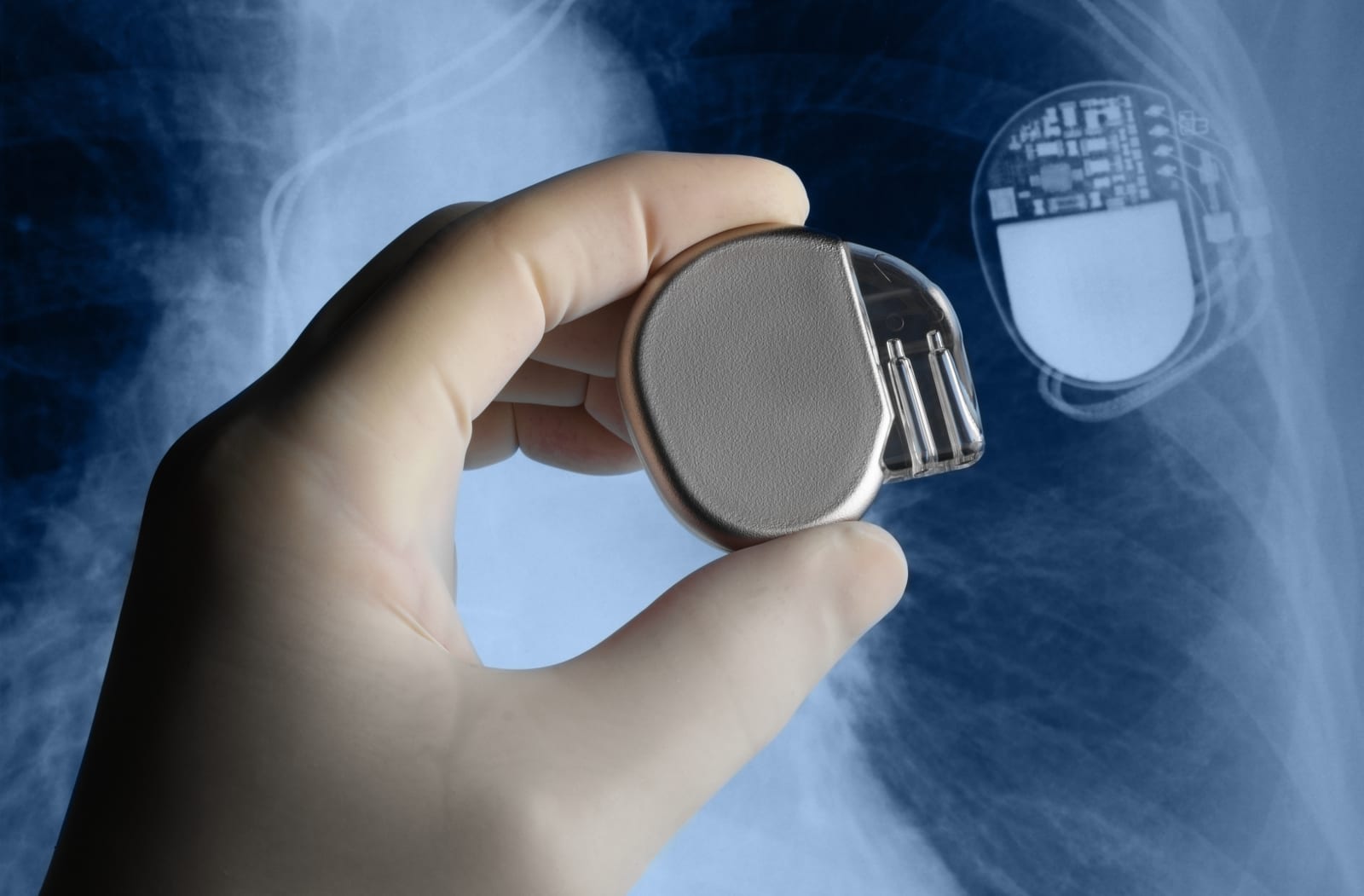
Pacemakers are far more vulnerable to hacking than we thought
Back in January, the FDA has finally acknowledged that some pacemakers and other cardiac devices are vulnerable to hacking. But how vulnerable are they, exactly? A security company called WhiteScope has discovered 8,000 bugs that hackers can exploit in pacemaker programmers — the tools used to adjust and monitor the device itself — from four different manufacturers. More importantly, the researchers said they’ve also discovered that pacemakers don’t authenticate programmers, so any working tool listed on eBay has the potential to harm patients with the implant.
Manufacturers are supposed to control programmers’ distribution, but the researchers themselves got their test devices from the auction website for as little as $500 to as much as $3,000. In addition to those issues, the team has found that doctors’ monitoring systems don’t require log-in names and passwords when pacemakers connect to them. They even found unencrypted patients’ data stored in the tools, including SSNs, names, phone numbers and medical conditions.
That said, Matthew Green, an Assistant Professor for Computer Science at Johns Hopkins, noted that doctors are adamant not to let security systems block patient care. He said that requiring passwords would merely lead to a “post-it note on the device listing the password,” so every doctors’ staff member can access the data they need. Green also called attention to some dubious parts of the study, particularly the lack of emphasis on the team’s most alarming finding that third-party programmers can remotely access pacemakers:
All of the other issues are kind of peripheral. If you can use your own hardware to send programming commands to a device… 7/n
— Matthew Green (@matthew_d_green) May 24, 2017
Despite the points Green raised, it’s still true that various security researchers have been warning manufacturers about pacemakers’ and other cardiac devices’ vulnerabilities for years. Unfortunately, it sounds like very few listened: a separate study by security firm Ponemon Institute LLC found that only 17 percent of manufacturers took steps to secure their products. While we’ve yet to hear about an incident that has led to a patient’s death, it’s still ideal to make cardiac devices more secure as cyberattacks become more common, elaborate and sophisticated.
(13)